Payara Platform 5 Community Edition Supports HTTP/2 on All JDK Versions
Published on 24 Jul 2020
by Matthew Gill
Topics:
Payara Server 5,
JakartaEE
|
0 Comments
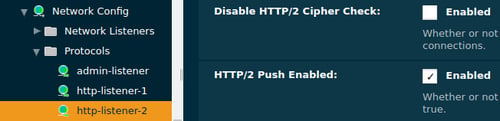
Payara Platform 5 brought with it an implementation of Servlet 4.0, which itself contains support for the HTTP/2 standard. HTTP/2 support in Java has been fairly obscure for JDK 8 users, causing issues for many depending on their JDK minor version. This blog hopes to clarify the state of HTTP/2 in Payara Platform 5.
If you just want a quick answer to which Payara versions support HTTP/2 on which JDK version, jump ahead to Does Payara Server Support HTTP/2?
The New Release of Payara Platform is Here!
Published on 16 Jun 2020
by Matthew Gill
Topics:
What's New,
MicroProfile,
JakartaEE,
New Releases
|
0 Comments
We're happy to announce that Payara Platform Community (5.2020.2) and Payara Platform Enterprise (5.20.0) Editions are out today! The Community Release includes 28 bug fixes, 13 improvements, 3 new features, and 5 component upgrades. You can download it here!
Here's some detail of what's included in the 5.2020.2 Community release:
Certificate Realm Changes in Payara Server 5.192
Published on 08 Aug 2019
by Matthew Gill
Topics:
Payara Platform 5
|
5 Comments
What is a Security Realm?
A security realm in Payara Server is a component used to authenticate users. Despite all the complicated terminology used in Java EE security, which is not helped by different application servers having their own terminology to describe the same thing, that's fundamentally all it is. The 'certificate' realm is a Payara Platform-specific component used to authenticate users using a certificate store. This will be used, for example, in client certificate authentication.
What Is Kubernetes and How Does It Relate to Docker?
Published on 14 Jun 2019
by Matthew Gill
Topics:
Payara Micro,
Docker,
Kubernetes
|
0 Comments
Kubernetes is most commonly used with Docker managed containers, although it doesn't strictly depend on it. Kubernetes defines a Container Runtime Interface (CRI) that container platforms must implement in order to be compatible. These implementations are colloquially known as "shims". This makes Kubernetes platform agnostic so that instead of Docker you're free to use other platforms with corresponding shims, such as CRI-O or KataContainers.
OpenJDK Support FAQs
Published on 22 Jan 2019
by Matthew Gill
Topics:
JDK 8,
OpenJDK
|
0 Comments
As of this month, there will no longer be any public JDK 8 releases. This means that security fixes won't be publicly accessible. A Payara support contract lets you take advantage of Payara's partnership with Azul, providing you with access to Zulu Enterprise. This means that you will have access to all future JDK 8 security fixes. Below are some common questions we receive regarding Zulu Enterprise and how it works with a Payara support contract.
Monitoring Payara Server with JConsole
Published on 13 Nov 2018
by Matthew Gill
Topics:
Monitoring
|
0 Comments
JConsole is a useful tool for monitoring Java processes. You can collect data from a Java process such as: heap memory usage, thread count, CPU usage, classes loaded and MBean data. This allows you to gauge whether any Java process is using too much system resources. This guide will show you how to monitor Payara as a local process (on the same machine), or a remote process. This blog will assume that you've got a valid JDK and Payara install.
Did You Know? Payara Support Gives you Access to Zulu Enterprise & JDK Support!
Published on 08 Nov 2018
by Matthew Gill
Topics:
Payara Platform 5,
Payara Support,
JDK 8,
OpenJDK
|
0 Comments
Did You Know? Payara Micro Allows Deploying Directly from Maven Central!
Published on 15 Oct 2018
by Matthew Gill
Topics:
Maven,
Payara Micro,
Payara Platform 5
|
0 Comments
Session Replication in Payara Server with Hazelcast
Published on 30 Aug 2018
by Matthew Gill
Topics:
Payara Server Basics - Series,
Payara Server 5 Basics
|
7 Comments
*Note: This blog post is an update to Dynamic Clustering and Failover on Payara Server With Hazelcast, which was written for Payara Server 4.
Introduction
This article continues our introductory blog series on setting up a simple deployment group with Payara Server, carrying straight on from our last blog where we configured sticky sessions for Payara Server.
Configuring Sticky Sessions for Payara Server with Apache Web Server
Published on 27 Aug 2018
by Matthew Gill
Topics:
Payara Server Basics - Series,
Payara Server 5 Basics
|
2 Comments
*Note: This blog post is an update to Configuring Stick Sessions for Payara Server with Apache Web Server, which was written for Payara Server 4.
Introduction
This article continues our introductory blog series on setting up a simple deployment group with Payara Server, carrying straight on from our last blog where we set up a load balancer for our deployment group.