Payara Platform Supports TLS 1.3 on JDK 8
Published on 13 Mar 2020
 by Susan Rai
by Susan Rai
Transport Layer Security (TLS) was introduced as a replacement for Secure Sockets Layer (SSL). TLS is a cryptographic protocol which provides secure communication between a client and a server. It also provides a mechanism by which information is not tampered with, falsified or read by anyone other than the intended receiver. TLS 1.3 was released in August 2018 to replace the widely used TLS 1.2. TLS 1.3 comes with stronger cryptographic algorithms and brings in major improvements in performance, security and privacy, which will be discussed in this blog.
Why TLS 1.3?
TLS 1.3 compromised backward compatibility for proper security design. It was built from the ground up and removed a host of features that were responsible for vulnerability in TLS 1.2, such as Static RSA handshake, CBC MtE modes (this was responsible for Lucky 13 and POODLE etc.), RC4 and Renegotiation. They have also simplified some of the existing features and added new features to significantly improve performance, privacy and security.
Improvement in Performance
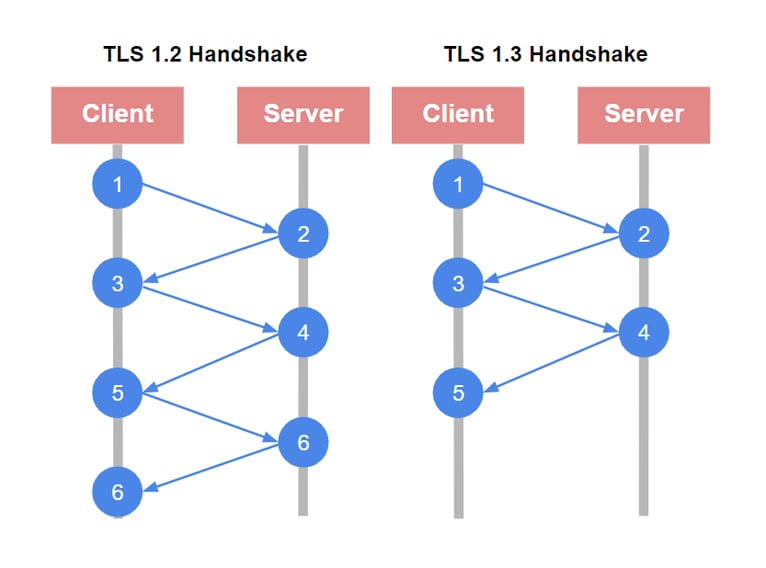
Establishing a handshake in TLS 1.2 requires two round trips before starting to send HTTP call to interact with a server, first to choose the cipher suite it is going to use, and then to exchange the certificates and key share. Although in reality each trip only adds delays ranging in around hundreds of milliseconds to complete the handshake, research has shown that delay of even 250ms is enough negatively impact the user experience and make them think about trying a different website.
With TLS 1.3 most of the handshake can be established with just one round trip. This has a positive effect on the network resources that are required for a client to communicate with a server, roughly cutting the encryption latency in half. Making TSL 1.3 lot faster than TLS 1.2.
 Another improvement in performance is that the resumption doesn't require a round trip. When a client and server successfully establish a TLS handshake for the first time, both of them store a shared encryption key locally. This key will be used in the future when the client visits the server again. The client can send encrypted data in its first message to the server, without performing the handshake. This is done using Session Ticket (PSK) with the encrypted key share which the server and client have agreed to previously, it uses this key to send the data back. This has the same latency as the HTTP because initial handshakes are no longer needed.
Another improvement in performance is that the resumption doesn't require a round trip. When a client and server successfully establish a TLS handshake for the first time, both of them store a shared encryption key locally. This key will be used in the future when the client visits the server again. The client can send encrypted data in its first message to the server, without performing the handshake. This is done using Session Ticket (PSK) with the encrypted key share which the server and client have agreed to previously, it uses this key to send the data back. This has the same latency as the HTTP because initial handshakes are no longer needed.
Improvement in Security
Throughout the years, TLS 1.2 has had numerous high profile vulnerabilities that have exploited parts of the handshake protocol that were badly designed and used outdated algorithms. TLS 1.3 completely redesigned the handshake protocol eliminating all of the issues faced by previous versions.
It also removed many of the vulnerable components such as Static RSA handshake, where if the certificate key was leaked, everything stored in the past could be decrypted, which is a huge problem because certificates are kept for years. Other components that were removed were vulnerable ciphers like CBC MtE modes and RC4. These ciphers were responsible for numerous attacks, such as Vaudenay, Lucky 13 and POODLE, but were only supported in TLS 1.2 for backward compatibility.
Payara Platform Supports TLS 1.3 on JDK 8 with Zulu
Nearly all the production Java applications are based on Java 8. But the TLS 1.3 was only included in JDK 11 and later versions, support for it was not backported to JDK 8. With Payara Platform, support for TLS 1.3 is available with Zulu JDK 8. Zulu JDK includes OpenJSSE TLS 1.3 JSSE provider, which can be used to enable TLS 1.3 support without any code changes. The OpenJSSE provider can also be used programmatically to code to TLS 1.3 and RSASSA-PSS capabilities not directly available via the Java 8 APIs. Read more on how to enable TLS 1.3 in JDK 8.
Since Payara Server 4 has entered the Maintenance Lifecycle, support for TSL 1.3 on JDK 8 is only available to Payara Platform Enterprise customers. Learn more on the benefits of becoming a Payara Enterprisecustomer.
Related Posts
Boost Developer Productivity with Payara Server Maven Plugin + AI Agent
Published on 12 Sep 2025
by Gaurav Gupta
0 Comments
Managing Payara Server Just Got Smarter
Imagine managing your Jakarta EE applications not just with Maven goals, but by asking natural questions.
With the experimental AI Agent built into the Payara Server Community's Maven Plugin, you can ...
Securing Jakarta EE Application Servers Needs Executive Attention
Published on 10 Sep 2025
by Asif Khan
0 Comments


%20Application%20Servers-An%20Executive%20Guide%20Cover.jpg?width=500&name=Securing%20Jakarta%20EE%20(Java%20EE)%20Application%20Servers-An%20Executive%20Guide%20Cover.jpg)