GlassFish to Payara Server Migration - migrating away from the Oracle Access Manager integration
Originally published on 09 Feb 2017
Last updated on 05 Oct 2020
 by Fabio Turizo
by Fabio Turizo
In the fifth part of our continuing series on alternatives for commercial Oracle GlassFish features, we are looking at a replacement for the Oracle's Access Manager integration feature.
What is Oracle Access Manager?
Oracle GlassFish Server includes a special security provider, implemented as a custom JASPIC (JSR-196, Java Authentication Service Provider Interface for Containers) module that allows enterprise applications to authenticate and take advantage of the Single Sign On functionality provided by its integration with Oracle Access Manager (a security suite with strong integration with other Oracle products and several infrastructure arrangements). This security provider can be used in the following 2 ways:
- As an authenticator module, using the standard Java EE
BASIC,FORMor client certificate (CERT) mechanisms; delegating authentication to the Access Manager. - As an identity verifier that redirects the user to the Oracle Access Manager Web Gate (a login or startup page) in case of authentication failure. It also eases the login process by maintaining a single session across several applications (SSO).
How can it be replaced?
Since Oracle Access Manager is a proprietary licensed product of Oracle, there’s no special integration that comes bundled with Payara Server. However, Payara Server itself contains a simple Single Sign On solution inherited from GlassFish Open Source Edition that can be easily configured when using the standard JAAS configuration.
To enable this feature on Payara Server, go to the server-config → Virtual Server section and select the virtual servers used by your applications:
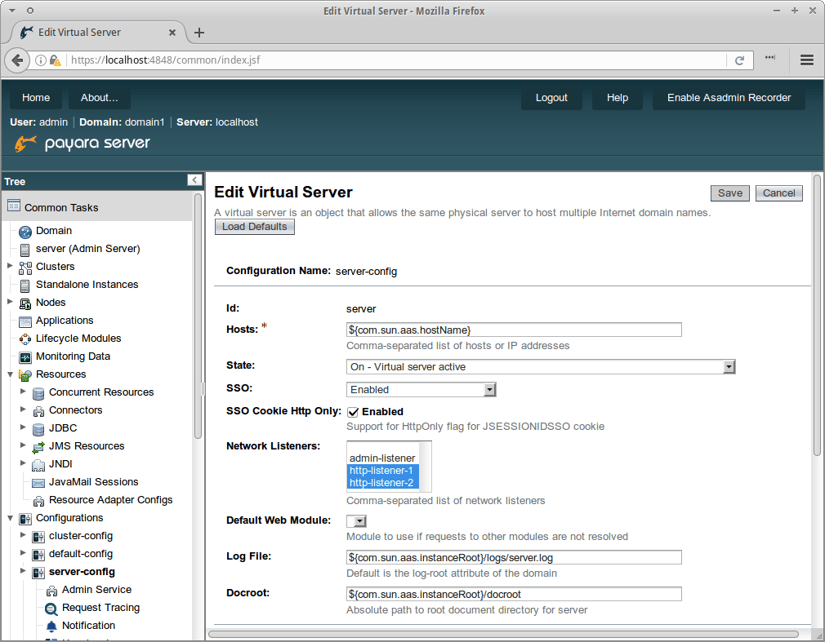
On the SSO property, select Enabled and configure the listeners that will be used for establishing the Single-Sign-On session (by default the standard HTTP and HTTPS listeners of the domain or instance configuration). Make sure to also set the sso-max-inactive-seconds and sso-reap-interval-seconds additional properties to the time frames that a SSO session will use before expiring.
When Single Sign On is enabled, all web applications that are deployed on the same virtual server will share authentication state, so if a user logs in to a web application he will be implicitly logged for all other remaining applications that require the same authentication information as well. Keep in mind that this behavior only applies for web applications configured on the same security realm.
If you were using Oracle Access Manager with your GlassFish Server and require a strong identity and access management suite of tools with good support that can be integrated with Payara Server, we strongly recommend migrating to ForgeRock’s suite of products and replace Oracle Access Manager with their own management suite.
Considering that the access management application (Open AM) doesn’t have direct support for Payara Server, to fully integrate it and its SSO capabilities, please follow the instructions we have detailed in our 'Forge Rock Integration with Payara Server' blog series:
Related Posts
Securing Jakarta EE Application Servers Needs Executive Attention
Published on 10 Sep 2025
by Asif Khan
0 Comments
Why Java Developers Need to Help Their CTO Prioritise Security in 2025
Published on 26 Aug 2025
by Asif Khan
0 Comments

%20Application%20Servers-An%20Executive%20Guide%20Cover.jpg?width=500&name=Securing%20Jakarta%20EE%20(Java%20EE)%20Application%20Servers-An%20Executive%20Guide%20Cover.jpg)
