Configuring SSL/TLS Certificates with Payara Server and Let's Encrypt
Published on 21 Dec 2018
 by Mark Wareham
by Mark Wareham
To run your application or server over HTTPS you're going to need a certificate. Commonly referred to as an SSL or TLS certificate, this is a guide on how to register one using Let's Encrypt's Certbot and then how to configure Payara Server to use it.
For the purposes of this example, the environment is as follows, but many other combinations will work:
- Amazon Linux based EC2 instance registered to a public domain name.
- Payara Server 5 installed on the above EC2 instance.
Installing Certbot
Certbot is still in 'Experimental' stage with Amazon Linux, so to install it, I followed the Certbot install instructions:
wget https://dl.eff.org/certbot-auto
chmod a+x certbot-auto
Installed the dependencies https://certbot.eff.org/docs/contributing.html#notes-on-os-dependencies myself using yum.
Then started up certbot with the --no-bootstrap option
sudo ./certbot-auto --no-bootstrap
Generating the Certificate
For this next step you'll need to ensure your server is accessible on port :80 for the challenge. This is because Let's Encrypt's servers hit your FQDN for to confirm you currently own it.
Because my setup is not using a web server such as Apache, I run certbot specifying the option --standalone. This is tells certbot which method to use for the challenge. I also specify the domain that the ec2 instance is associated with.
./certbot-auto certonly --standalone -d yourec2publicdomain.com
The output indicates where certbot says it saved the cert files. In this folder there'll be a fullchain.pem which contains the certificate, and privkey.pem which is the private key. Make a note of this location.
Putting the New Certificate into the Keystore
To insert these keys into the keystore in my specific Payara Server domain (for example, production, domain1), I first need to create a keystore. Then import that keystore into the keystore within Payara Server. This is done using keytool, which is provided in a JDK.
The keystore within Payara Server has a default password of "changeit". If you have changed it, then you'll need to use the password you changed it to. To keep things simple and because a later step requires it, I keep all the passwords the same.
To create a keystore I first had to convert the files to a .pkcs12 file:
openssl pkcs12 -export -in /etc/letsencrypt/live/yourFQDNhere/fullchain.pem -inkey /etc/letsencrypt/live/yourFQDNhere/privkey.pem -out pkcs.p12 -name letsencrypt
I then converted that to a keystore:
keytool -importkeystore -deststorepass changeit -destkeypass changeit -destkeystore letsencrypt.jks -srckeystore pkcs.p12 -srcstoretype PKCS12 -srcstorepass changeit
Now to import the newly generated keystore into the existing one:
Move to your $PAYARA_HOME/glassfish/domains/production/config directory. If you're not using the production domain then you'll need to substitute this folder in the path with your domain's name.
keytool -importkeystore -srckeystore /path/to/new/keystore/letsencrypt.jks -destkeystore keystore.jks
Configuring Payara to use the keystore
1. Visit the admin console (Default is on port :4848).
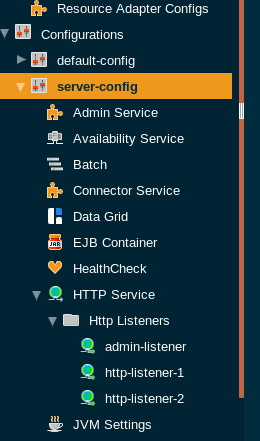
2. Now navigate to Configurations-> server-config ->HTTP Service -> Http Listeners - > http-listener-2 (listener 2 is for HTTPS)
4. Enter into certificate nickname "letsencryptcrt", and into key store "letsencrypt.jks"
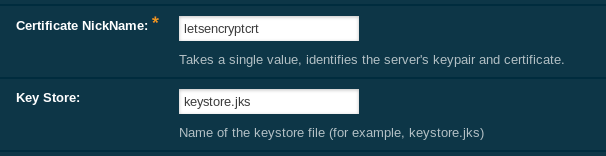
5. Hit Save.
6. Restart the domain for the changes to take effect. This is done from the CLI (substitute the domain name with your own if needed)
asadmin restart-domain production
7. Test your changes by visiting your FQDN on HTTPS and checking for the presence of a certificate (Payara Server default port is :8181)
For more information on application and application server security, see our security topic on our blog.
Want help with security? Check out support options from Payara Services:

