Payara Server LDAP Integration - Part 1: Configuring the LDAP Server
Published on 04 Nov 2016
 by Fabio Turizo
by Fabio Turizo
If you work in an organization with a robust IT department, it's very likely that you are using a LDAP server to handle your user directory information. You probably have to follow some general guidelines dictating that all web applications deployed within the organization’s infrastructure must access this user directory; and must authenticate and authorize the users that will interact with them. This is a very common scenario nowadays.
In this three-parts article series I will illustrate the implementation of the LDAP integration using a sample scenario: integrate Payara Server with a LDAP user directory and manage the authentication and authorization of a sample web application.
Starting the LDAP Server
There are many different LDAP server implementations in the market today (in both commercial and open source models). For our scenario, we will quickly start an OpenDJ instance using a Docker container and set up a directory domain with some test users and groups.
First, we start with a new Docker image that will download the OpenDJ binaries and run them in a container. This is a Java based image, since OpenDJ needs the JDK to run:
FROM java:8
MAINTAINER Fabio Turizo <fabio.turizo@payara.fish>
WORKDIR /opt
ENV JAVA_HOME /usr/lib/jvm/java-8-openjdk-amd64/
ENV MVN_REPO=https://maven.forgerock.org/repo/repo/org/forgerock/opendj
ENV OPENDJ_VERSION=3.0.0
ENV SERVER_PATH opendj-server-legacy
RUN curl $MVN_REPO/$SERVER_PATH/$OPENDJ_VERSION/$SERVER_PATH $OPENDJ_VERSION.zip \
-o /tmp/opendj.zip && \
unzip /tmp/opendj.zip -d /opt && \
rm /tmp/opendj.zip
ADD run.sh /opt/opendj/run.sh
ADD users.ldif /opt/opendj/initial.ldif
EXPOSE 1389 4444
WORKDIR /opt/opendj
CMD ["./run.sh"]
You will notice that we are using 2 external files in this image: run.sh and users.ldif. Let’s start with the users.ldif file, which we are using to create a starting set of users and groups:
dn: dc=payara,dc=fish
objectClass: top
objectClass: domain
dc: payara
dn: cn=Alfa Michael,dc=payara,dc=fish
objectClass: organizationalPerson
objectClass: top
objectClass: person
objectClass: inetOrgPerson
uid: malfa
mail: malfa@payara.fish
givenName: Michael
sn: Alfa
cn: Alfa Michael
userPassword: {SSHA}nirDyc9/XKLXqUqlR3sqD1De3qhybUqZQeU8pg==
creatorsName: cn=Directory Manager,cn=Root DNs,cn=config
dn: cn=Beta Carol,dc=payara,dc=fish
objectClass: organizationalPerson
objectClass: top
objectClass: person
objectClass: inetOrgPerson
uid: cbeta
mail: cbeta@payara.fish
givenName: Carol
sn: Beta
cn: Beta Carol
userPassword: {SSHA}ALhq+r+G3znVsPH70FkzyhHRZiN092w1GXiAZw==
dn: cn=Omega John,dc=payara,dc=fish
objectClass: organizationalPerson
objectClass: top
objectClass: person
objectClass: inetOrgPerson
uid: jomega
mail: jomega@payara.fish
givenName: John
sn: Omega
cn: Omega John
userPassword: {SSHA}KVj0XDak6E+IRecFkkCveTzsmW014IlGN2LlWg==
dn: cn=Admins,dc=payara,dc=fish
objectClass: groupOfNames
objectClass: top
member: cn=Alfa Michael,dc=payara,dc=fish
description: Administrators
cn: Admins
entryUUID: b7f3af29-3834-4765-9978-33e419073a65
createTimestamp: 20161019012425Z
creatorsName: cn=Directory Manager,cn=Root DNs,cn=config
dn: cn=Common,dc=payara,dc=fish
objectClass: groupOfNames
objectClass: top
member: cn=Beta Carol,dc=payara,dc=fish
member: cn=Omega John,dc=payara,dc=fish
description: Common Users
cn: Common
entryUUID: 8bc4ac5c-3313-4f9d-a111-6c933191fb2d
createTimestamp: 20161019012453Z
creatorsName: cn=Directory Manager,cn=Root DNs,cn=config
The contents of this file will allow us to create an initial set of 3 users (Michal Alfa, Carol Beta and John Omega) and 2 groups (Admin and Common). These objects are under the dc=payara, dc=fish base domain name.
Finally, we have the run.sh file. This file handles the OpenDJ installation and initialization using bash scripting:
#!/usr/bin/env bash
cd /opt/opendj/
if [ ! -d ./data/config ] ; then
echo "Executing OpenDJ first setup"
MANAGER_USER=${MANAGER:-"cn=Directory Manager"}
BASE_DN=${BASE_DN:-"dc=payara,dc=fish"}
PASSWORD=${PW:-admin}
./setup --cli --hostname localhost --ldapPort 1389 --rootUserDN "${MANAGER_USER}" \
--rootUserPassword "${PASSWORD}" --backendType pdb --baseDN "${BASE_DN}" \
--ldifFile "/opt/opendj/initial.ldif" --acceptLicense --no-prompt \
--noPropertiesFile
else
echo "Starting OpenDJ"
./bin/start-ds
fi
if (bin/status -n -w "${PASSWORD}" | grep Started); then
echo "OpenDJ is running"
while true; do sleep 100000; done
fi
This bash script will detect if there’s a previous OpenDJ installation (by checking out if the local data directory ./data/config exists). If not, it will setup OpenDJ using the command line interface option of the setup binary utility. The script provides the values for the installation options (root user, root password, LDAP port, etc.), but some of them can be changed with environment variables (${MANAGER}, ${PASSWORD}, etc.). If OpenDJ is already installed, then the script will simply start the server.
Finally, we let the script run the container indefinitely by starting an infinite loop that sleeps the input at frequent intervals.
Now, we proceed to build this image:
docker build -t fturizo/opendj .
And then start a new container with it:
docker run -d -p 1389:1389 -v ~/opendj-data:/opt/opendj/data –-name=opendj fturizo/opendj
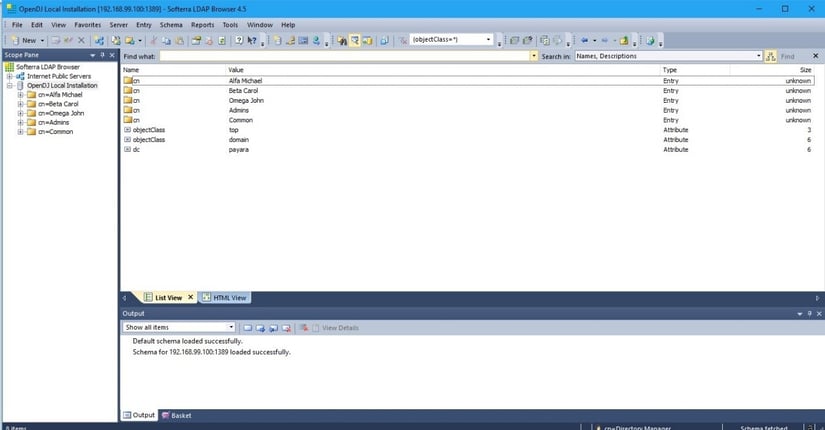
You can now connect to this LDAP server using port 1389. Using an LDAP Browser tool, we can check that our schema was imported correctly and the OpenDJ server is running:
Click here for Part 2, where we look at configuring LDAP Realm and creating a web application.
Click here for Part 3, where we go through the process of extracting user information.